How Stealth Addresses Work in Monero and Why XMR Receiver Addresses Are Hard to Trace
As on-chain analytics continue to improve, address association and fund path tracking have become defining features of public blockchains. Although most cryptocurrency addresses are made up of random strings, user activity can still be identified through transaction behavior, KYC data, and address clustering analysis.
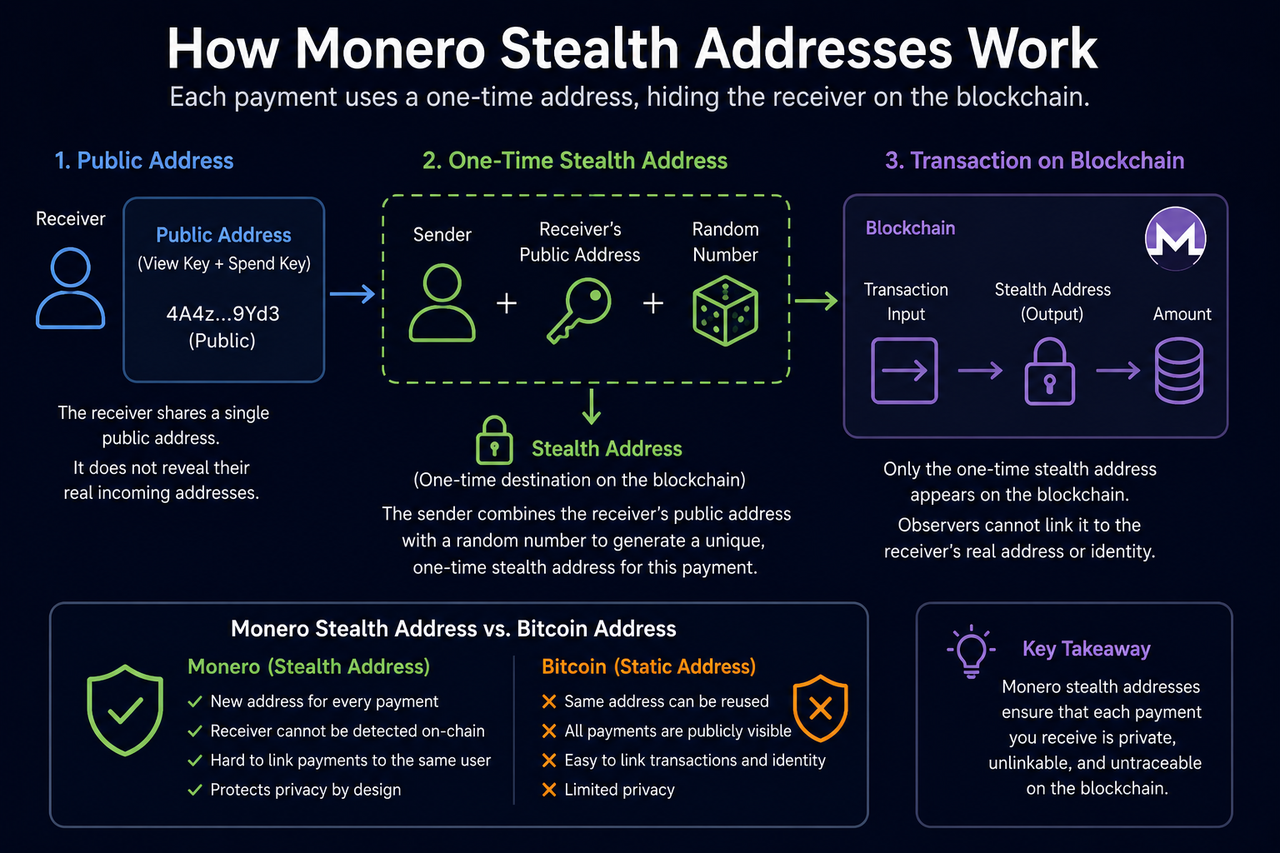
Against this backdrop, Stealth Addresses are widely regarded as a key component of Monero’s privacy system. Their core purpose is to prevent on-chain addresses from directly exposing a user’s identity and financial relationships.
What Is a Stealth Address?
A Stealth Address is a privacy mechanism used to hide the real receiving address.
In the Monero network, users have public wallet addresses, but each time they receive a transaction, the system automatically generates a new “one time address” for the on-chain record. Outside observers can see that a transaction output exists, but they cannot directly determine which real wallet the output belongs to.
As a result, even if the same user receives XMR multiple times, the same address will not repeatedly appear in on-chain records.
This design means that:
-
A wallet’s total balance cannot be viewed directly
-
Address relationships cannot be easily established
-
A full transaction history cannot be traced through a public address
The core function of a Stealth Address is to break the direct link between a “public address” and an “on-chain output.”
Why Does Monero Need to Hide Receiving Addresses?
On public blockchains such as Bitcoin, receiving addresses are often reused over long periods.
If a user publicly shares an address, for example, for payments, donations, or trading, anyone can view:
-
The address balance
-
Historical transfer records
-
The source and destination of funds
-
Transaction relationships with other addresses
This transparency improves auditability, but it also weakens privacy protection.
Monero aims to prevent public addresses from directly revealing a user’s financial situation. To do this, it uses Stealth Addresses to hide receiver identities and reduce the accuracy of address clustering and on-chain behavior analysis.
How Are Stealth Addresses Generated?
When a user receives a Monero transaction, the wallet does not directly use the public address. Instead, it dynamically generates a one time address.
This process mainly involves two components: the Public View Key and the Public Spend Key.
The sender uses the receiver’s public keys together with random data to generate a unique output address. This address corresponds only to the current transaction and cannot be reverse engineered by outside observers to reveal the real wallet address.
For on-chain analysts, each transaction output appears as a completely new independent address, making it difficult to determine whether multiple outputs belong to the same user.
What Role Does the View Key Play in Monero?
Although Stealth Addresses hide the real receiving address, users still need to view their own transaction history and balance.
To support this, Monero uses a View Key mechanism.
The main functions of a View Key include:
-
Scanning the blockchain for outputs that belong to the wallet
-
Viewing received transaction records
-
Verifying transaction status
-
Providing limited auditability
Users can selectively share a View Key, allowing a third party to view certain wallet information without being able to spend the funds.
This mechanism gives Monero a degree of balance between privacy protection and verifiability.
Why Can’t Monero Balances Be Viewed Like Bitcoin Balances?
In Bitcoin, addresses and on-chain outputs are publicly linked, so anyone can directly calculate an address balance.
Monero works differently.
Because Stealth Addresses generate a new output address for every transaction, outside observers cannot determine which outputs belong to the same wallet. As a result, they cannot accurately calculate the total balance.
Even if a user publicly shares their Monero address, others cannot use a blockchain explorer to directly view their full asset holdings.
This design improves financial privacy, but it also means the Monero blockchain cannot provide fully transparent account queries in the same way Bitcoin can.
What Is the Relationship Between Subaddresses and Stealth Addresses?
Subaddresses are a further extension of Monero’s privacy model.
Users can generate multiple subaddresses from the same wallet for:
-
Different receiving scenarios
-
Merchant payment management
-
Fund separation across platforms
-
Reducing address reuse risk
Although subaddresses themselves are visible to others, one time outputs are still generated on-chain through the Stealth Address mechanism. This means outside observers still have difficulty linking them together.
This design further strengthens Monero’s privacy flexibility.
How Are Stealth Addresses Different from Bitcoin’s Address Model?
Monero and Bitcoin differ clearly in how receiving addresses are designed.
| Comparison | Monero Stealth Address | Bitcoin Address |
|---|---|---|
| Address visibility | Real receiving address hidden | Address publicly visible |
| Address reuse | Avoided by default | Common |
| Balance lookup | Cannot be viewed directly | Can be viewed directly |
| Address clustering analysis | Relatively difficult | Relatively easy |
| Default privacy | Yes | No |
Bitcoin places greater emphasis on transparency and public verifiability, while Monero places greater emphasis on transaction privacy and address anonymity.
Do Stealth Addresses Mean Absolute Anonymity?
Stealth Addresses can improve address privacy, but they do not provide absolute anonymity.
Factors that may still affect privacy include:
-
Network layer data leaks
-
User behavior patterns
-
Transaction timing correlations
-
Links to KYC information
-
External payment records
In addition, privacy may be weakened if users voluntarily disclose transaction information or wallet data.
The core value of Stealth Addresses, therefore, is to increase the cost of on-chain analysis, not to eliminate every possible method of tracking.
Conclusion
Stealth Addresses are one of the core mechanisms in Monero’s (XMR) privacy system. Their main role is to hide the real receiving address in a transaction. By generating a one time address for every transaction, Monero reduces the accuracy of address clustering analysis and fund path tracking, improving user privacy protection.
At the same time, mechanisms such as View Keys and Subaddresses help Monero balance privacy protection, verifiability, and practical usability.
FAQs
Why Can’t Public Monero Balances Be Viewed?
Because Monero uses one-time output addresses, outside observers cannot determine which transactions belong to the same wallet, so they cannot accurately calculate the balance.
How Do Stealth Addresses Protect Privacy?
Stealth Addresses break the direct link between a public wallet address and on-chain outputs, reducing the effectiveness of address clustering analysis.
What Is a View Key?
A View Key is Monero’s viewing key. It is used to scan transaction records that belong to a wallet, but it does not grant permission to spend funds.
What Are Subaddresses Used For?
Subaddresses allow users to generate multiple receiving addresses for different payment scenarios while still maintaining privacy protection.
Are Stealth Addresses Completely Untraceable?
No. Stealth Addresses make on-chain analysis more difficult, but network behavior, external data, and user actions may still affect privacy.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?