What Are Monero Ring Signatures? How XMR Hides Transaction Senders
As on-chain analytics tools continue to mature, the traceability of public blockchains is becoming increasingly powerful. Although Bitcoin addresses are not directly tied to real world identities, transaction paths, address clustering, and links to KYC data can already be used to identify user behavior to some extent.
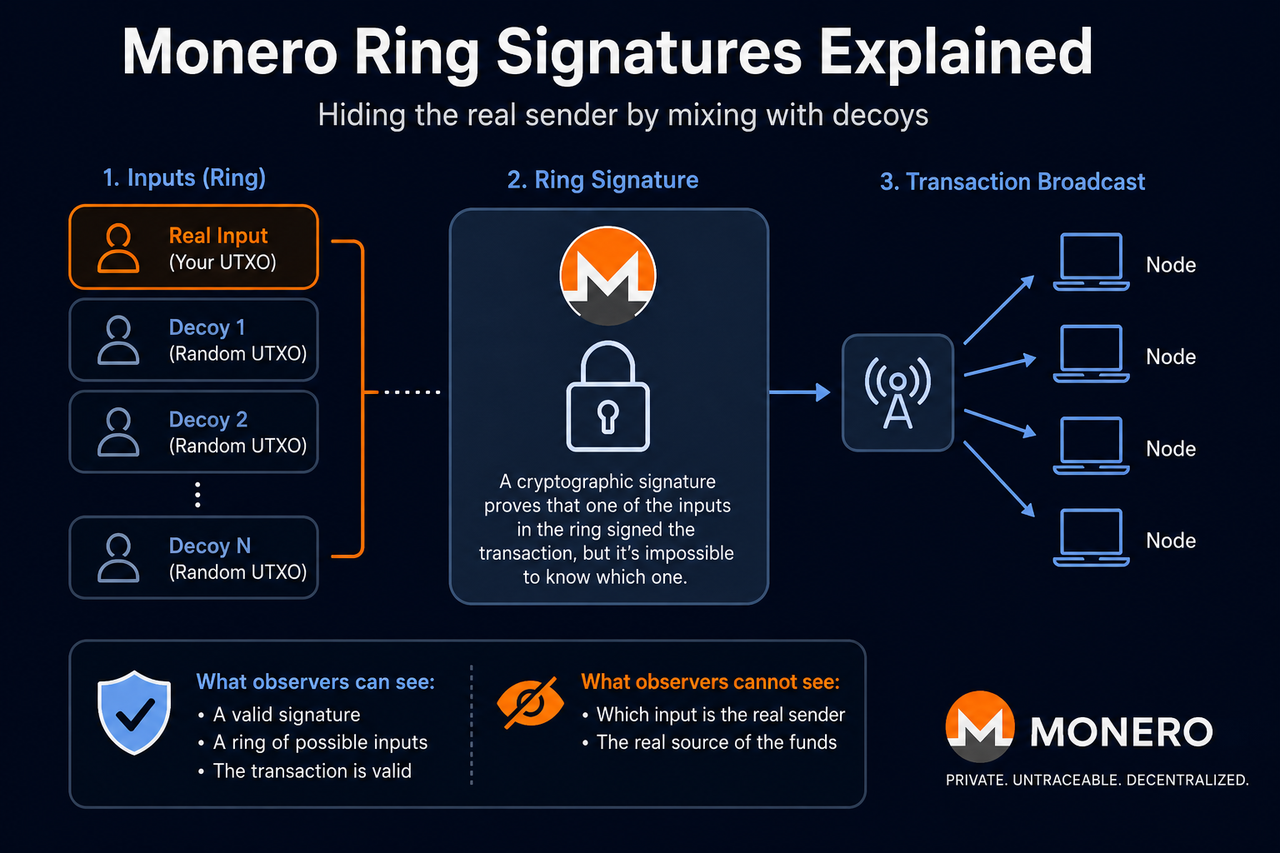
Ring Signatures are one of the most important anonymity mechanisms used by Monero, a cryptocurrency built around privacy protection. Unlike transparent public blockchains, Monero does not directly expose the real sender of a transaction. Instead, it mixes the real input with several historical transaction outputs, making it difficult for outside observers to accurately identify the source of funds.
What Are Ring Signatures?
Ring Signatures are a cryptographic signature mechanism designed to hide the identity of the real signer. In the Monero network, when a user initiates a transaction, the system does not sign only with the real input. Instead, it randomly selects multiple historical outputs from the blockchain and combines them with the real input to form a “ring.”
Validators can confirm that the transaction was initiated by one member of the ring and that the signature is valid, but they cannot determine exactly which member is the real sender. This design makes the source of Monero transactions difficult to trace directly.
Unlike traditional digital signatures, Ring Signatures do not require the real signer’s identity to be revealed. Instead, they emphasize anonymity within a group. Monero’s anonymity, therefore, does not come from hiding the existence of a transaction itself, but from hiding the real source of the input.
Why Does Monero Need to Hide Transaction Senders?
One of the defining features of public blockchains is transparency. Bitcoin, for example, permanently records all transaction inputs and outputs on-chain, allowing anyone to view fund flows, address balances, and historical transaction records.
Although addresses are usually strings of characters, blockchain analytics companies can build user profiles through address associations, transaction behavior, and fund movement patterns. Once a user is linked to exchange KYC data, the traceability of a public ledger becomes even stronger.
Monero aims to reduce this analyzability, which is why it introduced Ring Signatures to obscure transaction sources. By hiding the real input, Monero reduces the accuracy of address clustering and fund tracking, thereby improving user privacy.
How Do Ring Signatures Work?
When a user initiates a Monero transaction, the wallet first selects a real spendable output as the transaction input. The system then randomly selects several other outputs from historical blockchain records as decoys and combines them with the real input to form a signature ring.
The wallet generates a single signature for the entire input set. From an outside observer’s perspective, it is possible to confirm that the transaction was initiated by one member of the ring, but not to identify which input is real.
After the transaction is broadcast to the network, nodes verify whether the signature is valid and confirm that no double spending has occurred, but they do not reveal the real source of the funds. As a result, unlike Bitcoin, where fund paths can be viewed directly, Monero transaction inputs are hidden inside an anonymity set.
What Is an Anonymity Set?
An anonymity set refers to the group of all possible candidates that could be the real sender in a transaction.
For example, if a ring contains 16 outputs, outside observers can only know that the real input may be one of those 16 outputs, but they cannot determine which one. In theory, the larger the anonymity set, the harder on-chain analysis becomes and the stronger the transaction privacy.
Monero has continued to increase its default ring size over time to strengthen its overall anonymity. Because all transactions use Ring Signatures by default, the entire network can share a larger anonymity pool, rather than relying on a small number of anonymous transactions to create isolated privacy sets.
How Does a Key Image Prevent Double Spending?
Although Ring Signatures hide the real input, the network still needs to prevent the same funds from being spent more than once.
To achieve this, Monero uses a Key Image mechanism. Each real output generates a unique Key Image when it is spent. This identifier cannot be used to reverse engineer the real address, but the network can check whether it has already been used.
If the same Key Image appears again, it means the corresponding funds have already been spent, and the transaction will be rejected by the network. This design allows Monero to prevent double spending without revealing the real input.
How Does the CLSAG Upgrade Improve Ring Signatures?
Early versions of Monero used the MLSAG, or Multilayered Linkable Spontaneous Anonymous Group, structure to handle Ring Signatures.
The network later upgraded to CLSAG, or Concise Linkable Spontaneous Anonymous Group, to improve verification efficiency and reduce transaction data size.
The main advantages of CLSAG are smaller transaction size, faster verification, and lower fees. For the Monero network, this upgrade improved on-chain performance and scalability while preserving privacy.
How Are Ring Signatures Different from Bitcoin’s UTXO Model?
Both Monero and Bitcoin operate on a UTXO model, but their transaction privacy logic is clearly different.
| Comparison | Monero Ring Signatures | Bitcoin UTXO |
|---|---|---|
| Input source | Hidden by default | Fully public |
| Transaction tracing | Highly difficult | Directly analyzable |
| Address association | Difficult to cluster | Easy to cluster |
| Default privacy | Yes | No |
| on-chain transparency | Lower | Higher |
Bitcoin places greater emphasis on public transparency and verifiability, while Monero places greater emphasis on transaction anonymity and privacy protection.
Do Ring Signatures Mean Complete Anonymity?
Ring Signatures make on-chain tracking much harder, but they do not mean transactions are “absolutely impossible to analyze.”
Factors that can affect privacy include the quality of decoy selection, user transaction behavior, network layer data leaks, and links to external KYC information. In addition, the smaller default ring size used in earlier versions of Monero once reduced its anonymity.
For this reason, Monero’s goal is not to achieve absolute anonymity, but to strengthen privacy protection by increasing the cost of on-chain analysis.
Conclusion
Ring Signatures are a core technology in Monero’s (XMR) privacy system. Their main role is to hide the identity of the real transaction sender. By mixing the real input with multiple historical outputs, Monero can form an anonymity set, reducing the accuracy of address association analysis and fund path tracking.
At the same time, the Key Image mechanism prevents double spending without revealing the real input, while the CLSAG upgrade further improves transaction efficiency and network performance.
FAQs
Why Does Monero Use Ring Signatures?
Monero uses Ring Signatures to reduce transaction traceability and prevent on-chain analytics tools from directly identifying the source of funds.
What Is an Anonymity Set?
An anonymity set is the group of candidate outputs within a ring that could be the real sender. In general, the larger the anonymity set, the stronger the privacy.
How Do Ring Signatures Prevent Double Spending?
Monero uses the Key Image mechanism to detect repeated spending, preventing double spending attacks while keeping the real input hidden.
What Is CLSAG?
CLSAG is an upgraded version of Monero’s Ring Signature mechanism. It reduces transaction size, improves verification efficiency, and lowers fees.
Do Ring Signatures Mean Complete Anonymity?
No. Ring Signatures make transactions harder to trace, but network behavior, KYC data, and statistical analysis may still affect privacy.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?