How does Mask Network transmit encrypted messages? A detailed breakdown of the technical workflow
In traditional internet social environments, user chat histories, images, and private data are typically stored in plaintext or in formats that can be decoded by centralized servers. This means platform operators—and even potential hackers—may access users' private communications. As Web3 privacy awareness grows, users urgently need a communication method that preserves their social connections while enabling full control over their own data.
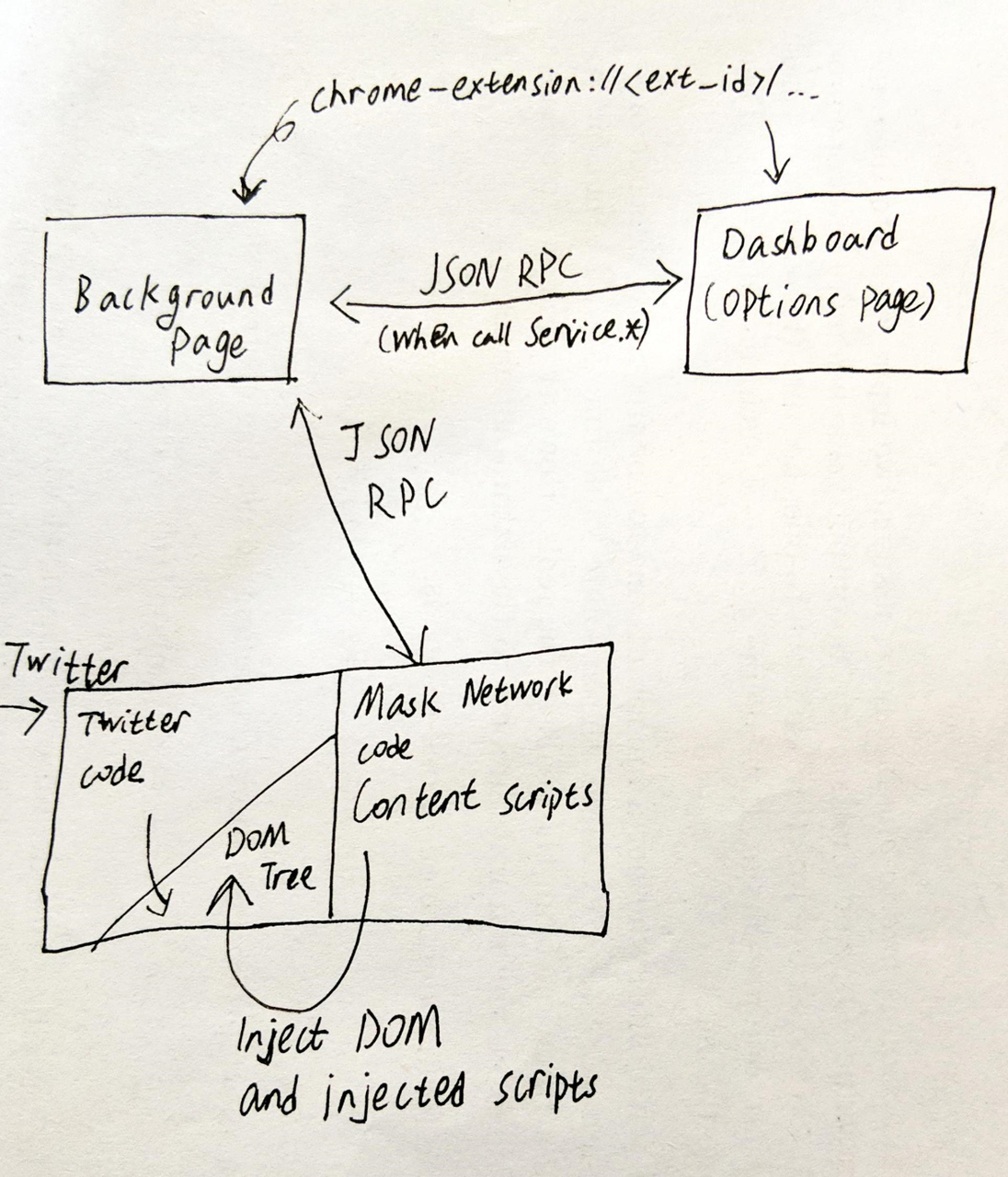
Mask Network acts as a privacy protection layer in this landscape. Rather than altering the underlying code of existing social platforms, it uses middleware technology to overlay an encryption solution at the application layer. This approach ensures social platforms function solely as “untrusted intermediaries” and “ciphertext storage,” with true decryption authority residing entirely in the user's Private Key.
Core Workflow of Mask Network Encrypted Transmission
Mask Network employs a sophisticated hybrid encryption protocol, broken down into four key steps:
-
Identity Initialization and Key Generation
When users install the Mask plugin and create or import a Wallet, the system generates a Public Key and Private Key pair based on the Secp256k1 curve. The Public Key is automatically synchronized to Mask’s decentralized identity (DID) network for others to retrieve, while the Private Key is securely stored locally on the user's device and never uploaded.
-
Sender Encryption Processing (Obfuscation and Packaging)
When a user drafts an encrypted tweet on Twitter, the process is as follows:
- Symmetric Encryption of Content: The system randomly generates an AES key, encrypting the tweet, images, and other content into ciphertext.
- Asymmetric Encryption of the Key: The sender retrieves the recipient’s (or a designated group’s) Public Key and uses it to encrypt the AES key.
- Posting Ciphertext: Mask transforms these encrypted data packets (including encrypted content and the wrapped key) into a string of seemingly random characters, automatically populating the social platform’s input box for posting.
-
Social Platform as Medium
The social platform (such as Twitter) treats this string as ordinary Text status for distribution. Without access to the Private Key, the platform’s servers see only an indecipherable hexadecimal data stream.
-
Recipient Decryption and Recovery
When the intended recipient refreshes the webpage, the Mask plugin automatically scans the page content:
- Ciphertext Recognition: The plugin identifies specific encrypted markers.
- Private Key Decryption: The plugin uses the recipient’s local Private Key to decrypt the wrapped AES key.
- Plaintext Recovery: With the decrypted AES key, the main content is decrypted and the plaintext is displayed directly in the user’s social interface.
Key Technical Components: GunDB and IPFS
To ensure decentralization and censorship resistance, Mask Network incorporates distributed storage technologies:
- GunDB: A decentralized graph database that synchronizes users' Public Key information and some encrypted indexes without relying on centralized servers.
- IPFS/Arweave: When users send large files or images, Mask uploads them to a decentralized storage network and posts only the encrypted storage Hash on the social platform, ensuring the platform cannot easily delete the data.
Summary
Mask Network’s encrypted message transmission mechanism effectively builds a “safe box inside a transparent glass room (Web2 social platform).” By combining mature cryptographic algorithms (AES, Secp256k1) with cutting-edge decentralized storage (IPFS), it strikes a balance between user experience and security. Users can enjoy end-to-end privacy protection without needing to understand complex technical details—this is Mask Network’s core competitive edge as a Web3 gateway.
Frequently Asked Questions (FAQs)
Does Mask Network store my chat records?
No. Mask Network follows a non-custodial model. Message content is posted on third-party social platforms, and the Private Key required for decryption is stored locally on your device. Mask Network cannot view or store your plaintext records.
Why does my encrypted message appear as a string of random characters?
That’s the result of encryption. For users or platform operators without the plugin or decryption rights, only the encrypted hexadecimal characters are visible. Only authorized users with the plugin can view the original information.
If I lose my Private Key, can I recover encrypted messages?
No. Since Mask Network uses end-to-end encryption and does not store user Private Keys, losing your Private Key means no one can decrypt previously posted encrypted content. Be sure to properly back up your seed phrase or Private Key.
Does encrypted transmission incur Gas fees?
Sending encrypted Text and images does not require Gas fees, as it primarily relies on the social platform’s text interface. However, if you send interactions involving on-chain Assets—such as encrypted Gift Coins or NFTs—you’ll need to pay the relevant chain’s Gas fees.
Related Articles
Reshaping Web3 Community Reward Models with RWA Yields

An Overview of Musk's Love-Hate Relationship with DOGE

A Beginner's Guide to the SuperRare NFT Market

Gate Research: Exploring the SocialFi Landscape in 2024: Insights on the Path Forward, Market Trends, and Future Directions

Top 10 Chinese Crypto Podcasts for 2025


