Ripple Releases XRPL Post-Quantum Migration Roadmap: Blockchain Approaches the Dawn of the Quantum-Secure Era
XRPL Post-Quantum Roadmap Released
Ripple has recently unveiled the post-quantum migration roadmap for XRP Ledger (XRPL), aiming to transition the entire network to post-quantum cryptography (PQC) by 2028. Unlike traditional on-chain upgrades that rely on patchwork fixes, this initiative is a comprehensive overhaul across accounts, signatures, and verification logic, spanning approximately 3–4 years and explicitly incorporating emergency contingencies for extreme scenarios.
To clarify the core strategy, focus on three key concepts:
-
Gradual migration: Progresses in phases to mitigate systemic risks from abrupt transitions.
-
Parallel operation: Maintains coexistence of legacy and new cryptographic assumptions for a period to reduce ecosystem friction.
-
Emergency switch: Reserves a rapid convergence path for potential "quantum leaps" in computational capability.
XRPL is proactively building an adaptive trust infrastructure, rather than waiting passively for quantum threats to materialize.
Background and Timeline: Why Quantum Threats Are Now a Real Concern
Major public blockchains—including Bitcoin, Ethereum, and XRPL—have long depended on elliptic curve cryptography (ECC) and discrete logarithm assumptions. Shor’s algorithm in quantum computing theoretically undermines these systems. What elevates the issue from academic risk to engineering and governance priority is a practical attack vector: Harvest Now, Decrypt Later. Adversaries can collect on-chain public keys and ciphertext today, then attempt to derive private keys and access assets in the future as quantum computational power becomes feasible.
This has shifted the security focus:
-
Risks are not confined to the day quantum computing matures.
-
Prolonged exposure of sensitive data on-chain may have already started the countdown.
-
Industry debate has moved from "will it happen" to "how soon must it be taken seriously."
Technical Breakdown: XRPL’s Four-Stage Migration Plan
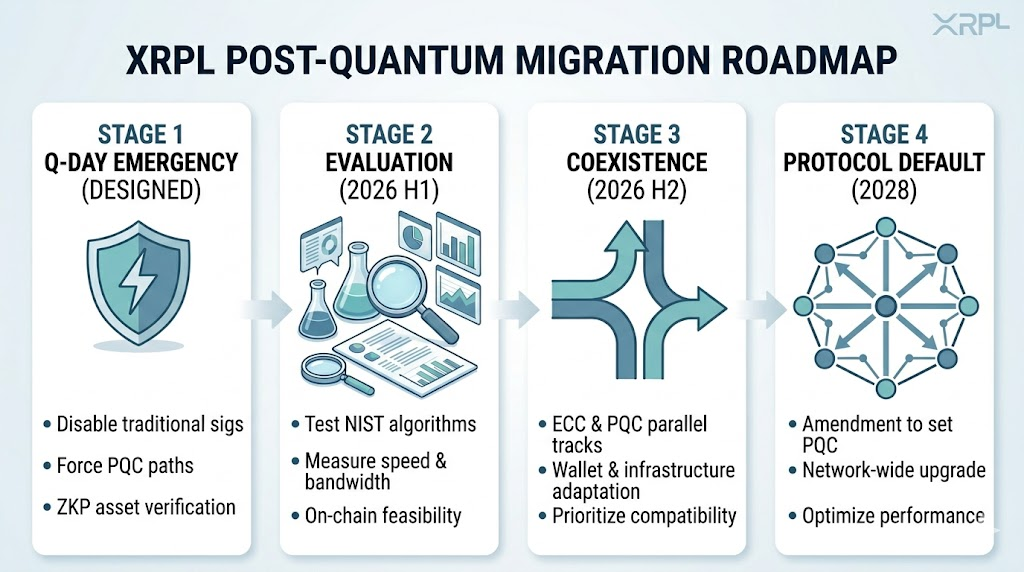
XRPL deliberately avoids a single, abrupt transition. The roadmap is structured into four evolutionary stages:
-
Q-Day emergency mechanism (already designed): If quantum capabilities leap forward, the network can swiftly disable traditional signatures, enforce post-quantum verification, and leverage zero-knowledge proofs to validate asset ownership—ensuring control is not directly compromised even in worst-case scenarios.
-
First half of 2026: Algorithm evaluation and experimentation: Testing NIST-recommended post-quantum algorithms (such as lattice schemes and hash signatures), with emphasis on signature size, verification speed, bandwidth consumption, and node hash rate requirements—addressing the question, "Is this viable in real-world blockchain environments?"
-
Second half of 2026: Parallel operation: ECC and PQC run concurrently, enabling wallets, applications, and infrastructure to adapt gradually. The focus here is on minimizing friction, not speed.
-
2028: Protocol-level final transition: Post-quantum solutions become protocol defaults via amendment, completing the network upgrade while continuously optimizing performance bottlenecks, node load, and network stability.
Key Technical Challenges: PQC and Blockchain Compatibility
Post-quantum cryptography typically exchanges higher on-chain costs for stronger long-term security, with main challenges in three areas:
-
Signature size: ECDSA signatures are typically tens to hundreds of bytes, while many PQC signatures can reach kilobyte scale, increasing transmission and storage demands.
-
Verification performance: Greater computational complexity may slow verification, impact throughput, and raise hardware requirements for nodes.
-
State expansion: Larger keys and signatures accelerate on-chain data growth, posing structural challenges for operations and decentralization costs over time.
Collectively, this is not just "adopting a safer algorithm," but renegotiating the balance between performance, security, and decentralization.
Security Model Evolution: From "Preventing Hackers" to "Anticipating Future Computing Paradigms"
Traditional security has focused on vulnerabilities, private keys, and consensus attacks. Post-quantum migration introduces a new axis: cryptographic assumptions themselves may fail in the future. This adds a clear time dimension to the security model—short-term defense against adversaries and implementation flaws, mid-term protection against systemic design and governance failures, and long-term provision for upgrades in response to paradigm shifts. XRPL’s roadmap is notable for translating this long-term perspective into actionable timelines and mechanisms.
Industry Comparison: Why XRPL Leads the Way
XRPL’s early progress is attributed to several structural advantages:
-
Flexible accounts and permissions: Key rotation and multisignature capabilities mean "changing keys" does not require "moving assets," clarifying migration paths.
-
Manageable upgrade coordination: Compared to highly fragmented and governance-stagnant chains, XRPL’s amendment process makes implementation more predictable.
-
Greater sensitivity to long-term security: Institutional use cases—payments and cross-border settlement—demand higher compliance, custody, and long-term trust, making phased migration more acceptable.
It's important to note that "leading the way" does not mean zero risk; it simply makes uncertainty visible earlier and spreads costs over a longer timeframe.
Risks and Uncertainties: Technical, Ecosystem, and Timing Factors
Even with a clear roadmap, uncertainties persist at three levels:
-
Technical: Standards and algorithms are evolving; implementation and security boundaries require ongoing validation.
-
Ecosystem: If wallets, exchanges, custodians, and related applications are not synchronized, protocol upgrades may be "complete on-chain but incomplete for users."
-
Timing: Quantum computing progress is unpredictable; Q-Day could arrive much sooner or later, affecting the likelihood and timing of emergency mechanisms.
Industry Evolution Along Quantum Computing Trajectory
Three simplified scenarios illustrate industry divergence:
-
Baseline scenario (moderate quantum progress): XRPL proceeds as planned, the rest of the industry gradually follows, and post-quantum becomes a long-term, infrastructure-level upgrade theme.
-
Early breakthrough scenario (Q-Day accelerated): Networks with emergency design and parallel migration can quickly converge trust assumptions; unprepared chains may face cascading pressures in liquidity, custody, and cross-chain interoperability.
-
Long-term bottleneck scenario (PQC performance remains constrained): The industry may be locked in a prolonged struggle between security upgrades, cost, and throughput, with risks and technical debt persisting and migration timelines repeatedly recalibrated.
Investment and Industry Impact: Who Benefits, Who Bears the Burden
Structurally, this topic acts as a slow variable and credit premium/discount, rather than a short-term event catalyst. Likely beneficiaries include post-quantum cryptographic infrastructure, high-performance on-chain verification and proof capabilities, and wallets and custody systems with robust support for key rotation and new signature standards. Those under pressure include protocols and applications with unclear upgrade paths, high governance coordination costs, or heavy reliance on legacy signatures and difficult-to-migrate states.
Conclusion: A "Slow Variable" Is Transforming the Industry’s Foundation
XRPL’s post-quantum roadmap cannot be captured by short-term price movements; it is fundamentally rewriting the competitive rules for which chains remain trustworthy over a decade. The industry narrative is shifting from "applying cryptography to blockchains" to "designing chains as security systems resilient to future computational paradigms." Those who achieve this transition earlier and more reliably will be best positioned for the next wave of infrastructure competition.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?